VeraCrypt
VeraCrypt
詳細情報
| タイトル | VeraCrypt |
|---|---|
| URL | https://www.veracrypt.fr/en/Home.html |
| バージョン | ver 1.26.24 |
| 更新日 | 2025/06/01 |
| 追加日 | 2016/02/02 |
| 種別 | フリーソフト |
| 説明 | TrueCrypt 7.1aのソースコードを元に開発されているディスク暗号化ソフト。 |
レビュー
レビューはありません。
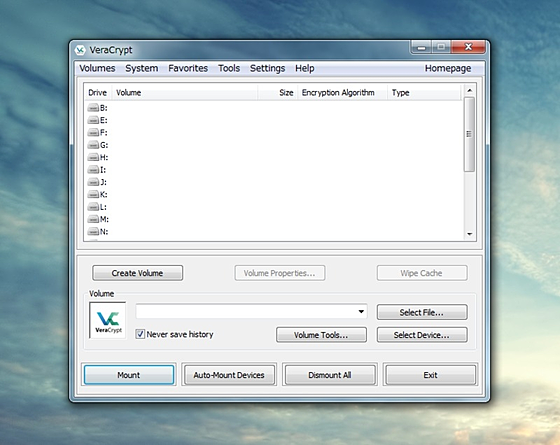
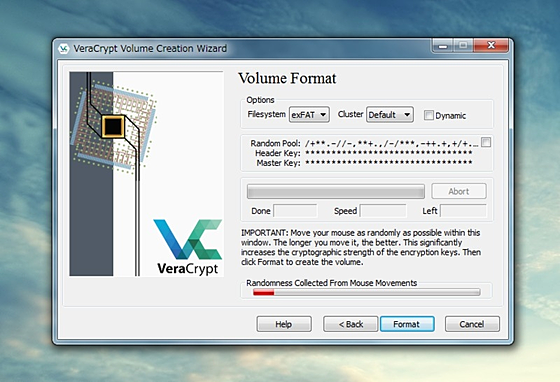
スクリーンショット
更新グラフ
バージョン履歴
差分がありません
Latest Stable Release - 1.26.20 (Monday February 3rd, 2025)
VeraCrypt Setup 1.26.20.exe
VeraCrypt_Setup_x64_1.26.20.msi
VeraCrypt Portable 1.26.20.exe
VeraCrypt_1.26.20_Windows_Symbols.zip
VeraCrypt_1.26.20.dmg (PGP Signature)
VeraCrypt_FUSE-T_1.26.20.dmg (PGP Signature)
veracrypt-1.26.20-setup.tar.bz2 (PGP Signature)
veracrypt-1.26.20-x86-legacy-setup.tar.bz2
veracrypt-1.26.20-Debian-12-amd64.deb (PGP Signature) and
veracrypt-1.26.20-Debian-12-i386.deb (PGP Signature)
veracrypt-console-1.26.20-Debian-12-amd64.deb (PGP Signature) and
veracrypt-console-1.26.20-Debian-12-i386.deb (PGP Signature)
veracrypt-1.26.20-Debian-11-amd64.deb (PGP Signature) and
veracrypt-1.26.20-Debian-11-i386.deb (PGP Signature)
veracrypt-console-1.26.20-Debian-11-amd64.deb (PGP Signature) and
veracrypt-console-1.26.20-Debian-11-i386.deb (PGP Signature)
veracrypt-1.26.20-Ubuntu-24.04-amd64.deb (PGP Signature)
veracrypt-console-1.26.20-Ubuntu-24.04-amd64.deb (PGP Signature)
(省略されました)
VeraCrypt Setup 1.26.20.exe
VeraCrypt_Setup_x64_1.26.20.msi
VeraCrypt Portable 1.26.20.exe
VeraCrypt_1.26.20_Windows_Symbols.zip
VeraCrypt_1.26.20.dmg (PGP Signature)
VeraCrypt_FUSE-T_1.26.20.dmg (PGP Signature)
veracrypt-1.26.20-setup.tar.bz2 (PGP Signature)
veracrypt-1.26.20-x86-legacy-setup.tar.bz2
veracrypt-1.26.20-Debian-12-amd64.deb (PGP Signature) and
veracrypt-1.26.20-Debian-12-i386.deb (PGP Signature)
veracrypt-console-1.26.20-Debian-12-amd64.deb (PGP Signature) and
veracrypt-console-1.26.20-Debian-12-i386.deb (PGP Signature)
veracrypt-1.26.20-Debian-11-amd64.deb (PGP Signature) and
veracrypt-1.26.20-Debian-11-i386.deb (PGP Signature)
veracrypt-console-1.26.20-Debian-11-amd64.deb (PGP Signature) and
veracrypt-console-1.26.20-Debian-11-i386.deb (PGP Signature)
veracrypt-1.26.20-Ubuntu-24.04-amd64.deb (PGP Signature)
veracrypt-console-1.26.20-Ubuntu-24.04-amd64.deb (PGP Signature)
(省略されました)
Latest Stable Release - 1.26.18 (Monday January 20th, 2025)
EXE Installer (x64 and ARM64):
VeraCrypt Setup 1.26.18.exe
MSI Installer (x64 only):
VeraCrypt_Setup_x64_1.26.18.msi
VeraCrypt Portable 1.26.18.exe
VeraCrypt_1.26.18_Windows_Symbols.zip
VeraCrypt_1.26.18.dmg (PGP Signature)
VeraCrypt_FUSE-T_1.26.18.dmg (PGP Signature)
veracrypt-1.26.18-setup.tar.bz2 (PGP Signature)
veracrypt-1.26.18-x86-legacy-setup.tar.bz2
veracrypt-1.26.18-Debian-12-amd64.deb (PGP Signature) and
veracrypt-1.26.18-Debian-12-i386.deb (PGP Signature)
veracrypt-console-1.26.18-Debian-12-amd64.deb (PGP Signature) and
veracrypt-console-1.26.18-Debian-12-i386.deb (PGP Signature)
veracrypt-1.26.18-Debian-11-amd64.deb (PGP Signature) and
veracrypt-1.26.18-Debian-11-i386.deb (PGP Signature)
veracrypt-console-1.26.18-Debian-11-amd64.deb (PGP Signature) and
veracrypt-console-1.26.18-Debian-11-i386.deb (PGP Signature)
(省略されました)
EXE Installer (x64 and ARM64):
VeraCrypt Setup 1.26.18.exe
MSI Installer (x64 only):
VeraCrypt_Setup_x64_1.26.18.msi
VeraCrypt Portable 1.26.18.exe
VeraCrypt_1.26.18_Windows_Symbols.zip
VeraCrypt_1.26.18.dmg (PGP Signature)
VeraCrypt_FUSE-T_1.26.18.dmg (PGP Signature)
veracrypt-1.26.18-setup.tar.bz2 (PGP Signature)
veracrypt-1.26.18-x86-legacy-setup.tar.bz2
veracrypt-1.26.18-Debian-12-amd64.deb (PGP Signature) and
veracrypt-1.26.18-Debian-12-i386.deb (PGP Signature)
veracrypt-console-1.26.18-Debian-12-amd64.deb (PGP Signature) and
veracrypt-console-1.26.18-Debian-12-i386.deb (PGP Signature)
veracrypt-1.26.18-Debian-11-amd64.deb (PGP Signature) and
veracrypt-1.26.18-Debian-11-i386.deb (PGP Signature)
veracrypt-console-1.26.18-Debian-11-amd64.deb (PGP Signature) and
veracrypt-console-1.26.18-Debian-11-i386.deb (PGP Signature)
(省略されました)
Latest Stable Release
Windows: Version 1.26.15 (Sunday, August 25th, 2024)
macOS/Linux: Version 1.26.14 (Monday, September 2nd, 2024)
VeraCrypt Setup 1.26.15.exe
VeraCrypt_Setup_x64_1.26.15.msi
VeraCrypt Portable 1.26.15.exe
VeraCrypt_1.26.15_Windows_Symbols.zip
Source Code: VeraCrypt 1.26.15 Source (Windows Zip)
(PGP Signature)
Windows: Version 1.26.15 (Sunday, August 25th, 2024)
macOS/Linux: Version 1.26.14 (Monday, September 2nd, 2024)
VeraCrypt Setup 1.26.15.exe
VeraCrypt_Setup_x64_1.26.15.msi
VeraCrypt Portable 1.26.15.exe
VeraCrypt_1.26.15_Windows_Symbols.zip
Source Code: VeraCrypt 1.26.15 Source (Windows Zip)
(PGP Signature)
Documentation
Latest Stable Release - 1.26.14 (Sunday August 25th, 2024)
VeraCrypt Setup 1.26.14.exe
VeraCrypt_Setup_x64_1.26.14.msi
VeraCrypt Portable 1.26.14.exe
VeraCrypt_1.26.14_Windows_Symbols.zip
macOS (Monterey 12 and later):
OSXFUSE compatible version :
VeraCrypt_1.26.14.dmg (PGP Signature)
FUSE-T compatible version :
VeraCrypt_FUSE-T_1.26.14.dmg (PGP Signature)
FUSE-T compatible version is recommanded for Mac computers with Apple silicon.
veracrypt-1.26.14-setup.tar.bz2 (PGP Signature)
veracrypt-1.26.14-x86-legacy-setup.tar.bz2
veracrypt-1.26.14-Debian-12-amd64.deb (PGP Signature) and
veracrypt-1.26.14-Debian-12-i386.deb (PGP Signature)
veracrypt-console-1.26.14-Debian-12-amd64.deb (PGP Signature) and
veracrypt-console-1.26.14-Debian-12-i386.deb (PGP Signature)
veracrypt-1.26.14-Debian-11-amd64.deb (PGP Signature) and
(省略されました)
Latest Stable Release - 1.26.14 (Sunday August 25th, 2024)
VeraCrypt Setup 1.26.14.exe
VeraCrypt_Setup_x64_1.26.14.msi
VeraCrypt Portable 1.26.14.exe
VeraCrypt_1.26.14_Windows_Symbols.zip
macOS (Monterey 12 and later):
OSXFUSE compatible version :
VeraCrypt_1.26.14.dmg (PGP Signature)
FUSE-T compatible version :
VeraCrypt_FUSE-T_1.26.14.dmg (PGP Signature)
FUSE-T compatible version is recommanded for Mac computers with Apple silicon.
veracrypt-1.26.14-setup.tar.bz2 (PGP Signature)
veracrypt-1.26.14-x86-legacy-setup.tar.bz2
veracrypt-1.26.14-Debian-12-amd64.deb (PGP Signature) and
veracrypt-1.26.14-Debian-12-i386.deb (PGP Signature)
veracrypt-console-1.26.14-Debian-12-amd64.deb (PGP Signature) and
veracrypt-console-1.26.14-Debian-12-i386.deb (PGP Signature)
veracrypt-1.26.14-Debian-11-amd64.deb (PGP Signature) and
(省略されました)
For those seeking support for the TrueCrypt format, please visit dedicated page for VeraCrypt version 1.25.9.
Latest Stable Release - 1.26.7 (Sunday October 1st, 2023)
VeraCrypt Setup 1.26.7.exe
VeraCrypt_Setup_x64_1.26.7.msi
VeraCrypt Portable 1.26.7.exe
VeraCrypt_1.26.7_Windows_Symbols.zip
macOS Monterey 12 and later:
VeraCrypt_1.26.7.dmg (PGP Signature)
OSXFUSE 4 or newer must be installed.
veracrypt-1.26.7-setup.tar.bz2 (PGP Signature)
veracrypt-1.26.7-x86-legacy-setup.tar.bz2
Debian 12:
veracrypt-1.26.7-Debian-12-amd64.deb (PGP Signature) and
veracrypt-1.26.7-Debian-12-i386.deb (PGP Signature)
veracrypt-console-1.26.7-Debian-12-amd64.deb (PGP Signature) and
veracrypt-console-1.26.7-Debian-12-i386.deb (PGP Signature)
Debian 11:
veracrypt-1.26.7-Debian-11-amd64.deb (PGP Signature)
veracrypt-console-1.26.7-Debian-11-amd64.deb (PGP Signature)
(省略されました)
Latest Stable Release - 1.26.7 (Sunday October 1st, 2023)
VeraCrypt Setup 1.26.7.exe
VeraCrypt_Setup_x64_1.26.7.msi
VeraCrypt Portable 1.26.7.exe
VeraCrypt_1.26.7_Windows_Symbols.zip
macOS Monterey 12 and later:
VeraCrypt_1.26.7.dmg (PGP Signature)
OSXFUSE 4 or newer must be installed.
veracrypt-1.26.7-setup.tar.bz2 (PGP Signature)
veracrypt-1.26.7-x86-legacy-setup.tar.bz2
Debian 12:
veracrypt-1.26.7-Debian-12-amd64.deb (PGP Signature) and
veracrypt-1.26.7-Debian-12-i386.deb (PGP Signature)
veracrypt-console-1.26.7-Debian-12-amd64.deb (PGP Signature) and
veracrypt-console-1.26.7-Debian-12-i386.deb (PGP Signature)
Debian 11:
veracrypt-1.26.7-Debian-11-amd64.deb (PGP Signature)
veracrypt-console-1.26.7-Debian-11-amd64.deb (PGP Signature)
(省略されました)
Latest Stable Release - 1.25.9 (Saturday February 19, 2022)
VeraCrypt Setup 1.25.9.exe (21.1 MB)
VeraCrypt_Setup_x64_1.25.9.msi (29 MB)
VeraCrypt Portable 1.25.9.exe (20.9 MB)
VeraCrypt_1.25.9_Windows_Symbols.zip (18.4 MB)
VeraCrypt_1.25.9.dmg (11.7 MB) (PGP Signature)
veracrypt-1.25.9-setup.tar.bz2 (41.5 MB) (PGP Signature)
veracrypt-1.25.9-x86-legacy-setup.tar.bz2 (13.8 MB)
veracrypt-1.25.9-Debian-11-amd64.deb (PGP Signature)
veracrypt-console-1.25.9-Debian-11-amd64.deb (PGP Signature)
veracrypt-1.25.9-Debian-10-amd64.deb (PGP Signature)
veracrypt-console-1.25.9-Debian-10-amd64.deb (PGP Signature)
veracrypt-1.25.9-Ubuntu-21.10-amd64.deb (PGP Signature)
veracrypt-console-1.25.9-Ubuntu-21.10-amd64.deb (PGP Signature)
veracrypt-1.25.9-Ubuntu-21.04-amd64.deb (PGP Signature)
veracrypt-console-1.25.9-Ubuntu-21.04-amd64.deb (PGP Signature)
veracrypt-1.25.9-Ubuntu-20.04-amd64.deb (PGP Signature)
veracrypt-console-1.25.9-Ubuntu-20.04-amd64.deb (PGP Signature)
veracrypt-1.25.9-Ubuntu-18.04-amd64.deb (PGP Signature)
(省略されました)
VeraCrypt Setup 1.25.9.exe (21.1 MB)
VeraCrypt_Setup_x64_1.25.9.msi (29 MB)
VeraCrypt Portable 1.25.9.exe (20.9 MB)
VeraCrypt_1.25.9_Windows_Symbols.zip (18.4 MB)
VeraCrypt_1.25.9.dmg (11.7 MB) (PGP Signature)
veracrypt-1.25.9-setup.tar.bz2 (41.5 MB) (PGP Signature)
veracrypt-1.25.9-x86-legacy-setup.tar.bz2 (13.8 MB)
veracrypt-1.25.9-Debian-11-amd64.deb (PGP Signature)
veracrypt-console-1.25.9-Debian-11-amd64.deb (PGP Signature)
veracrypt-1.25.9-Debian-10-amd64.deb (PGP Signature)
veracrypt-console-1.25.9-Debian-10-amd64.deb (PGP Signature)
veracrypt-1.25.9-Ubuntu-21.10-amd64.deb (PGP Signature)
veracrypt-console-1.25.9-Ubuntu-21.10-amd64.deb (PGP Signature)
veracrypt-1.25.9-Ubuntu-21.04-amd64.deb (PGP Signature)
veracrypt-console-1.25.9-Ubuntu-21.04-amd64.deb (PGP Signature)
veracrypt-1.25.9-Ubuntu-20.04-amd64.deb (PGP Signature)
veracrypt-console-1.25.9-Ubuntu-20.04-amd64.deb (PGP Signature)
veracrypt-1.25.9-Ubuntu-18.04-amd64.deb (PGP Signature)
(省略されました)
Bleeding edge builds based on latest source code are available at https://sourceforge.net/projects/veracrypt/files/VeraCrypt%20Nightly%20Builds/.
Latest Stable Release
For macOS and Windows: 1.25.7 (Friday January 7, 2022)
For FreeBSD and Linux: 1.25.4 (Friday December 3, 2021)
EXE Installer:
VeraCrypt Setup 1.25.7.exe (38.4 MB)
VeraCrypt_Setup_x64_1.25.7.msi (29.9 MB)
Limitation: MSI installer cannot be used if system partition is encrypted with VeraCrypt.
Portable version:
VeraCrypt Portable 1.25.7.exe (38.2 MB)
VeraCrypt_1.25.7_Windows_Symbols.zip (17.9 MB)
VeraCrypt_1.25.7.dmg (11.7 MB) (PGP Signature)
Debian 10 Buster:
Ubuntu 20.04:
GUI:
veracrypt-1.25.4-Ubuntu-20.04-arm64.deb (PGP Signature) and
veracrypt-1.25.4-Ubuntu-20.04-armhf.deb (PGP Signature)
Console:
veracrypt-console-1.25.4-Ubuntu-20.04-arm64.deb (PGP Signature) and
(省略されました)
Latest Stable Release
For macOS and Windows: 1.25.7 (Friday January 7, 2022)
For FreeBSD and Linux: 1.25.4 (Friday December 3, 2021)
EXE Installer:
VeraCrypt Setup 1.25.7.exe (38.4 MB)
VeraCrypt_Setup_x64_1.25.7.msi (29.9 MB)
Limitation: MSI installer cannot be used if system partition is encrypted with VeraCrypt.
Portable version:
VeraCrypt Portable 1.25.7.exe (38.2 MB)
VeraCrypt_1.25.7_Windows_Symbols.zip (17.9 MB)
VeraCrypt_1.25.7.dmg (11.7 MB) (PGP Signature)
Debian 10 Buster:
Ubuntu 20.04:
GUI:
veracrypt-1.25.4-Ubuntu-20.04-arm64.deb (PGP Signature) and
veracrypt-1.25.4-Ubuntu-20.04-armhf.deb (PGP Signature)
Console:
veracrypt-console-1.25.4-Ubuntu-20.04-arm64.deb (PGP Signature) and
(省略されました)
Latest Stable Release - 1.25.4 (Friday December 3, 2021)
EXE Installer for Windows XP, Windows 10 and later:
VeraCrypt Setup 1.25.4.exe (38.4 MB)
MSI Installer (64-bit) for Windows 10 and later:
VeraCrypt_Setup_x64_1.25.4.msi (29.9 MB)
Portable version for for Windows XP, Windows 10 and later:
VeraCrypt Portable 1.25.4.exe (38.2 MB)
VeraCrypt_1.25.4_Windows_Symbols.zip (17.9 MB)
macOS:
macOS Mavericks 10.9 and later:
VeraCrypt_1.25.4.dmg (11.7 MB) (PGP Signature)
OSXFUSE 3.10 or newer must be installed.
veracrypt-1.25.4-setup.tar.bz2 (41.5 MB) (PGP Signature)
veracrypt-1.25.4-x86-legacy-setup.tar.bz2 (13.8 MB)
Debian 11:
veracrypt-1.25.4-Debian-11-amd64.deb (PGP Signature)
Console:
veracrypt-console-1.25.4-Debian-11-amd64.deb (PGP Signature)
veracrypt-1.25.4-Debian-10-amd64.deb (PGP Signature)
(省略されました)
EXE Installer for Windows XP, Windows 10 and later:
VeraCrypt Setup 1.25.4.exe (38.4 MB)
MSI Installer (64-bit) for Windows 10 and later:
VeraCrypt_Setup_x64_1.25.4.msi (29.9 MB)
Portable version for for Windows XP, Windows 10 and later:
VeraCrypt Portable 1.25.4.exe (38.2 MB)
VeraCrypt_1.25.4_Windows_Symbols.zip (17.9 MB)
macOS:
macOS Mavericks 10.9 and later:
VeraCrypt_1.25.4.dmg (11.7 MB) (PGP Signature)
OSXFUSE 3.10 or newer must be installed.
veracrypt-1.25.4-setup.tar.bz2 (41.5 MB) (PGP Signature)
veracrypt-1.25.4-x86-legacy-setup.tar.bz2 (13.8 MB)
Debian 11:
veracrypt-1.25.4-Debian-11-amd64.deb (PGP Signature)
Console:
veracrypt-console-1.25.4-Debian-11-amd64.deb (PGP Signature)
veracrypt-1.25.4-Debian-10-amd64.deb (PGP Signature)
(省略されました)
Latest Stable Release: 1.24-Update7 (Friday August 7, 2020)
Installer for Windows 8 and later:
VeraCrypt Setup 1.24-Update7.exe (34.5 MB)
Portable version for Windows 8 and later:
VeraCrypt Portable 1.24-Update7.exe (34.3 MB)
Installer for Windows XP, Vista and 7:
VeraCrypt Legacy Setup 1.24-Update7.exe (34.5 MB)
(PGP Signature)
Portable version for Windows XP, Vista and 7:
VeraCrypt Legacy Portable 1.24-Update7.exe (34.3 MB)
(PGP Signature)
VeraCrypt_1.24-Update7_Windows_Symbols.zip (9.68 MB)
VeraCrypt_1.24-Update7.dmg (6.13 MB) (PGP Signature)
VeraCrypt_Legacy_1.24-Update7.dmg (9.39 MB) (PGP Signature)
veracrypt-1.24-Update7-setup.tar.bz2 (14.3 MB) (PGP Signature)
veracrypt-1.24-Update7-x86-legacy-setup.tar.bz2 (7.06 MB)
veracrypt-1.24-Update7-Debian-9-amd64.deb (PGP Signature)
veracrypt-console-1.24-Update7-Debian-9-amd64.deb (PGP Signature)
veracrypt-1.24-Update7-Debian-10-amd64.deb (PGP Signature)
(省略されました)
Installer for Windows 8 and later:
VeraCrypt Setup 1.24-Update7.exe (34.5 MB)
Portable version for Windows 8 and later:
VeraCrypt Portable 1.24-Update7.exe (34.3 MB)
Installer for Windows XP, Vista and 7:
VeraCrypt Legacy Setup 1.24-Update7.exe (34.5 MB)
(PGP Signature)
Portable version for Windows XP, Vista and 7:
VeraCrypt Legacy Portable 1.24-Update7.exe (34.3 MB)
(PGP Signature)
VeraCrypt_1.24-Update7_Windows_Symbols.zip (9.68 MB)
VeraCrypt_1.24-Update7.dmg (6.13 MB) (PGP Signature)
VeraCrypt_Legacy_1.24-Update7.dmg (9.39 MB) (PGP Signature)
veracrypt-1.24-Update7-setup.tar.bz2 (14.3 MB) (PGP Signature)
veracrypt-1.24-Update7-x86-legacy-setup.tar.bz2 (7.06 MB)
veracrypt-1.24-Update7-Debian-9-amd64.deb (PGP Signature)
veracrypt-console-1.24-Update7-Debian-9-amd64.deb (PGP Signature)
veracrypt-1.24-Update7-Debian-10-amd64.deb (PGP Signature)
(省略されました)
For Windows: 1.24-Update6 (Tuesday March 10, 2020)
VeraCrypt Setup 1.24-Update6.exe (34.5 MB)
VeraCrypt Portable 1.24-Update6.exe (34.3 MB)
VeraCrypt_1.24-Update6_Windows_Symbols.zip (9.51 MB)
VeraCrypt 1.24-Update6 Source (Windows Zip)
(PGP Signature) VeraCrypt DCS EFI Bootloader 1.24-Update6 Source
User Guide CHM: VeraCrypt 1.24-Update6 User Guide CHM (PGP
SHA256 sums for VeraCrypt 1.24-Update6 release files
SHA512 sums for VeraCrypt 1.24-Update6 release files
VeraCrypt Setup 1.24-Update6.exe (34.5 MB)
VeraCrypt Portable 1.24-Update6.exe (34.3 MB)
VeraCrypt_1.24-Update6_Windows_Symbols.zip (9.51 MB)
VeraCrypt 1.24-Update6 Source (Windows Zip)
(PGP Signature) VeraCrypt DCS EFI Bootloader 1.24-Update6 Source
User Guide CHM: VeraCrypt 1.24-Update6 User Guide CHM (PGP
SHA256 sums for VeraCrypt 1.24-Update6 release files
SHA512 sums for VeraCrypt 1.24-Update6 release files